Assuming you have your Microsoft Windows Domain Controllers sending their event logs into Splunk, here is a query that will pull out the pertinent details you need to find anything that is still running non-compliant RC4 for ticketing.
Note that your index and Log names may vary.
index="wineventlog" LogName="Security" EventCode IN ("4768", "4769", "4770", "4771")
| rex field=_raw "Account Information:\s*\r?\n(?:.*\r?\n)*?\s*MSDS-SupportedEncryptionTypes:\s*(?<acct_msds>[^\r\n]+)"
| rex field=_raw "Service Information:\s*\r?\n(?:.*\r?\n)*?\s*MSDS-SupportedEncryptionTypes:\s*(?<svc_msds>[^\r\n]+)"
| rex field=_raw "Domain Controller Information:\s*\r?\n(?:.*\r?\n)*?\s*MSDS-SupportedEncryptionTypes:\s*(?<dc_msds>[^\r\n]+)"
| rex field=_raw "(?s)Advertized Etypes:\s*(?<etype_section>.*?)(?:Additional Information:|Certificate Information:|Ticket information|$)"
| rex field=etype_section max_match=0 "(?<etypes>AES256-CTS-HMAC-SHA1-96|AES128-CTS-HMAC-SHA1-96|RC4-HMAC-NT-EXP|RC4-HMAC-OLD-EXP|RC4-HMAC-NT|DES-CBC-MD5|DES-CBC-CRC)"
| eval etypes=mvjoin(etypes, ", ")
| rename Ticket_Encryption_Type AS TicEncType
| rename Session_Encryption_Type AS SesEncType
| rename Pre_Authentication_EncryptionType AS PreAEncType
| eval ticket_type = case(
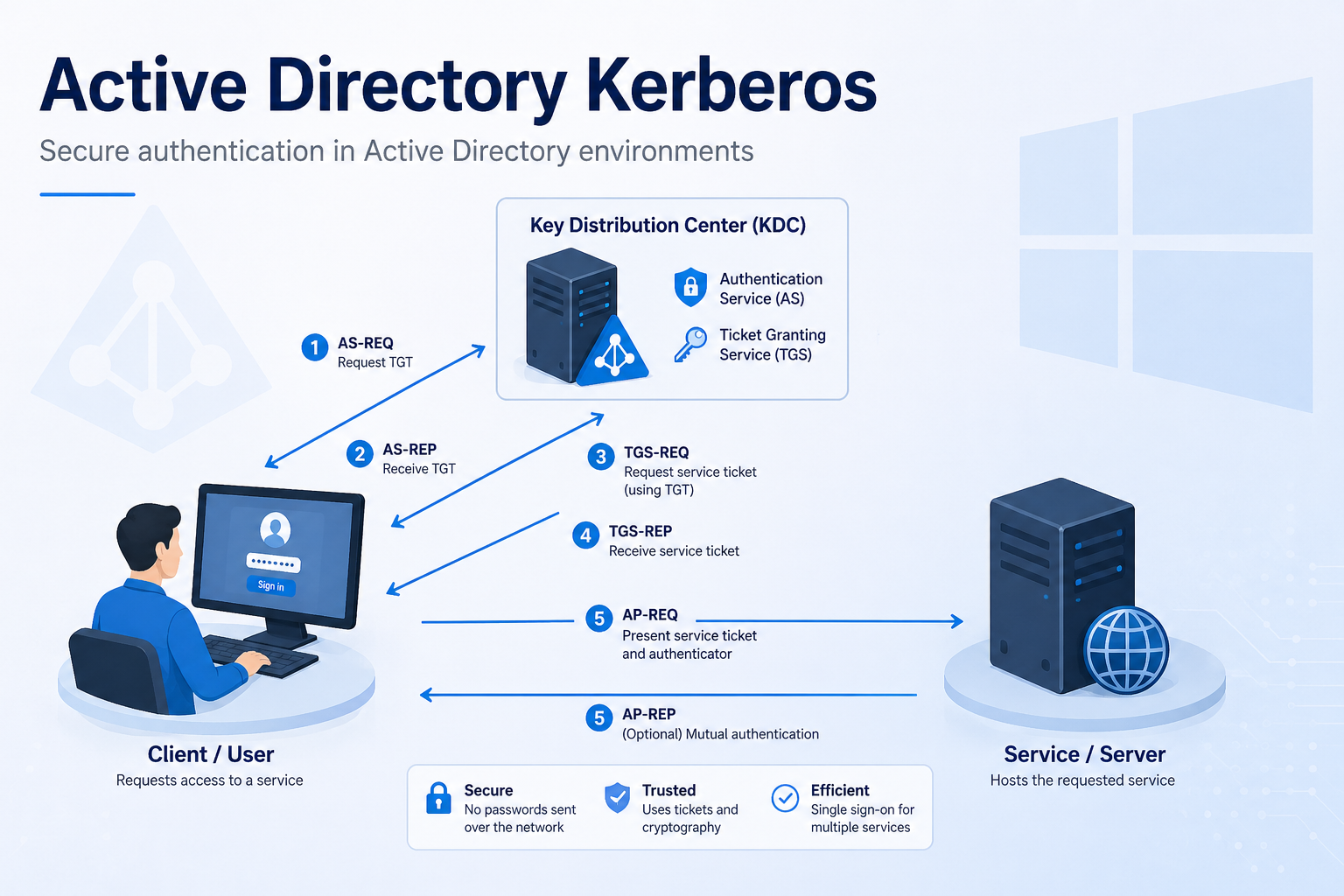
EventCode==4768, "AS-REQ (TGT)",
EventCode==4769, "TGS-REQ (TGS)",
EventCode==4770, "RENEWAL",
EventCode==4771, "Failure",
true(), "Other"
)
| sort - event_time
| search SesEncType = 0x17 OR TicEncType = 0x17 OR PreAEncType = 0x17 OR acct_msds = "RC4" OR svc_msds = "RC4" OR dc_msds = "RC4"
| table event_time Client_Address Account_Name Account_Domain service_name EventCode ticket_type TicEncType SesEncType PreAEncType Ticket_Options acct_msds svc_msds dc_msds etypes